The Billion $ Problem
Organizations heavily rely on email, making Business Email Compromise (BEC) one of the most common and costly threats. Attackers will perform email spoofing, phishing attacks, and use malware to take over legitimate email accounts and conduct unauthorized money transfers or steal confidential data.
Get Answers. Every Time.
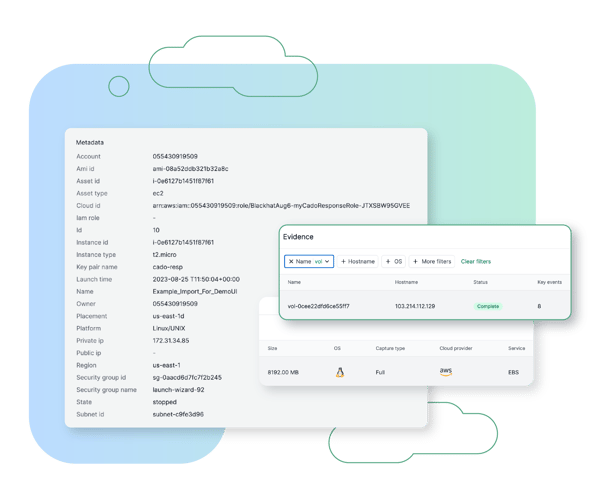
With Cado Security, analysts can investigate and respond to SaaS compromises, including Business Email Compromise (BEC), Account Takeover (ATO), and insider threats. Cado enables security teams to investigate key SaaS logs, such as Microsoft 365 UAL, alongside other sources captured across on-premises and cloud assets to gain a better understanding of the scope and impact of malicious activity.


Hear from our Customer, Agorà Security

“After testing out the product, the decision to purchase was a no brainer. Cado makes things simple.”
Director, Incident Response
Large Video Gaming Company

“The fact that I no longer have to wait 24 hours to start a forensics investigation is game changing.”
Digital Forensics and Incident Response Manager
Top Cybersecurity Consulting Firm

The Cado Advantage
Cado Security is helping organizations around the world achieve results.

Browse Other Use Cases
Explore other ways security teams are using the Cado platform to advance their mission.
Cross Cloud Investigations
Investigate incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
Endpoint Triage
Automate triage acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
Attack Containment
Perform response actions including stopping, containing, and isolating systems to prevent damage and spread.
Incident Response Preparedness
Assess your readiness to investigate and respond to threats, and establish a repeatable IR process.






