
Special Requirements Needed
Nation-state attacks are increasing in frequency and complexity, and new techniques are being employed to target hybrid infrastructure. Traditional tools and approaches for performing investigations are manual and too slow to keep up with present day attacks. Government organizations require the best security solutions available that provide automation and efficiency, especially when dealing with incidents in the cloud.
Never Compromise on Security
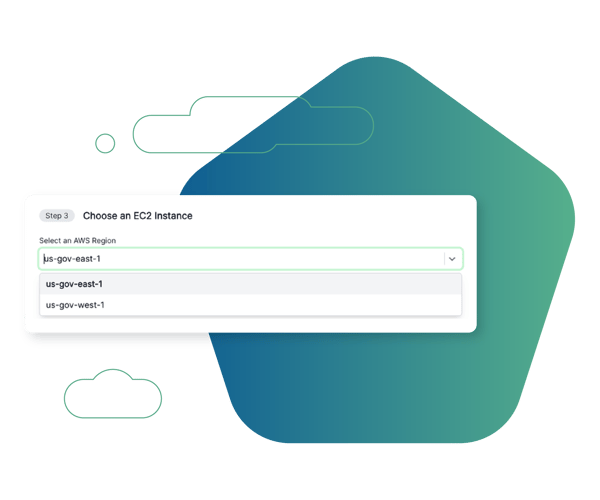
Cado Security enables government agencies to automate as much of the investigation process as possible. Deployed in AWS GovCloud, Cado delivers deep insights into risk quickly and securely. With Cado, government agencies can extend their incident response program to cloud, container, serverless, and SaaS environments.
Top Cado Use Cases
See how government agencies are using the Cado platform as a revolutionary investigation and response tool.
Cross Cloud Investigations
Respond to incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
SOC Triage
Automate triage acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
SaaS Investigations
Analyze SaaS logs alongside other critical sources to investigate compromises such as Business Email Compromise (BEC).
Cloud Detection & Response (CDR)
Marry threat detection with forensic context to expedite response.
Evidence Preservation
Ensure evidence residing in ephemeral environments is immediately captured and preserved before it disappears.






