Every Second Matters
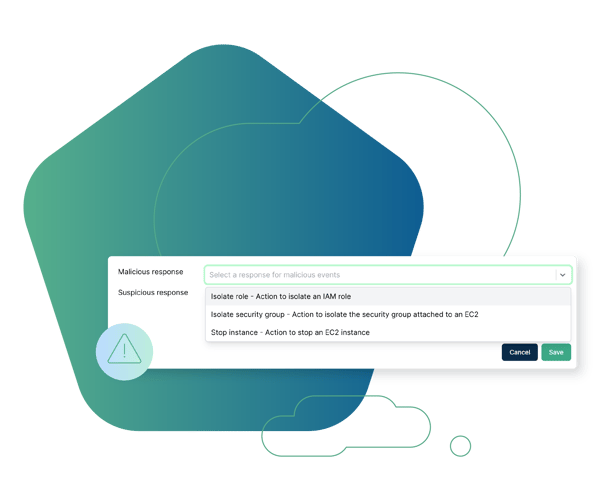
Having the ability to quickly take action and prevent damage and spread is critical to a robust incident response program. However, environments are constantly changing and can involve thousands of virtual machines, containers, and other services. This can make responding to threats in a timely manner overwhelming and in some cases impossible, especially when relying on manual techniques and processes alone.
Make Every Second Count
Cado Security delivers remediation capabilities, empowering analysts to quickly contain threats. Response actions can be taken manually or fully automated to ensure threats are contained around the clock – 24/7, 365. Users can define automated remediation actions, such as stopping or containing an instance, based on detection severity, environment tags, and more.


Hear from our Customer, Agorà Security

“The fact that we no longer have to manually request access to a potentially compromised system via our cloud team is a game changer.”
Incident Response Lead
Large Financial Instutition

“I can now confidently say I know what’s going on in my cloud.”
Cyber Security Incident Response Manager
Global Media Company

“After testing out the product, the decision to purchase was a no brainer. Cado makes things simple.”
Director, Incident Response
Large Video Gaming Company

The Cado Advantage
Cado Security is helping organizations implement containment strategies for incident response around the world.

Browse Other Use Cases
Explore other ways security teams are using the Cado platform to advance their mission.
Cross Cloud Investigations
Investigate incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
Endpoint Triage
Automate triage acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
BEC Investigations
Analyze SaaS logs alongside other critical sources to investigate compromises such as Business Email Compromise (BEC).
Incident Response Preparedness
Assess your readiness to investigate and respond to threats, and establish a repeatable IR process.






