Cloud, container, and serverless resources have transformed business development and deployment cycles, allowing companies to move at a much greater speed than ever before. However, businesses aren't the only ones taking advantage of the cloud. Threat actors have quickly evolved their tool kits to exploit cloud resources.
Attackers are Rapidly Evolving Their Tactics to Newer Cloud Services
In April last year, Denonia, the first publicly-known case of malware specifically designed to execute in an AWS Lambda environment, was discovered by the Cado Security Labs team. Although the first sample was fairly innocuous in that it only runs crypto-mining software, it demonstrates how attackers are using advanced cloud-specific knowledge to exploit complex cloud infrastructure, and is indicative of how we’re only scratching the surface of more nefarious attacks that may leverage a much wider range of cloud services.
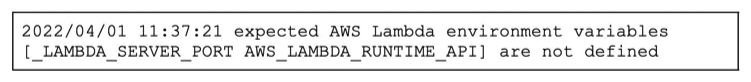
Lambda specific code from Denonia
With attackers rapidly evolving and innovating to find new ways to exploit cloud resources, security teams and organizations are struggling to keep up. Unfortunately, a lot of this has come down to the fact that technology hasn’t evolved fast enough. Until recently, security teams have been forced to apply legacy forensics and incident response approaches to the cloud, which has highlighted a major gap.
Struggling to Keep Up
89% of organizations have experienced a negative outcome in the time between detection and investigation of a cloud security incident according to ESG. Further, a recent report published by ISC2 stated that 67% of cybersecurity professionals are, at best, only moderately confident in their organization’s cloud security posture, and 43% observe a higher degree of risk in the cloud versus on-premises.
But why is managing risk in the cloud more complicated? The ESG report highlights that the speed at which security teams can access forensic data is a major issue, noting that 64% of cybersecurity professionals say it takes too much time to collect and process data to perform a timely investigation. As a result, over 1/3 of cloud security alerts are never investigated.
Is CIRA the Answer?
Cloud Investigation and Response Automation (CIRA) is an emerging category within cloud security. The category was first coined by Gartner® earlier this year and most recently included in the latest Hype Cycle for Workload and Network Security. CIRA technologies enable security teams to:
- Automate the collection and analysis of forensic data in cloud environments to expedite response
- Respond to threats that span multi-cloud environments, accounts, and resource types
- Preserve incident evidence in ephemeral environments consisting of services such as containers
- Adhere to incident and breach reporting requirements such as the SEC’s “Final Rule"
- Automate response actions so that damage and spread can be prevented without having human intervention
These capabilities empower organizations and security teams to seamlessly extend their incident response processes to the cloud. CIRA technology streamline forensic investigations, automating tasks from data capture and processing to analysis and response. There are a number of benefits associated with implementing CIRA technologies, including the ability to:
- Better manage cloud risk by extending visibility beyond what a traditional detection solution can provide
- Decrease costs associated with cloud investigations by reducing reliance on external service providers
- Close the cyber security skills gap by empowering analysts of all levels to perform forensics and incident response in the cloud
How Cado can Help
Cado is a CIRA platform that aims to automate as much of the incident response process as possible, from data capture and processing to root cause analysis and response. As a cloud-native platform, Cado enables security teams to gain immediate access to forensic-level data in multi-cloud, container, and serverless environments. Cado empowers security analysts of all levels to respond to cloud-based threats.
Interested in learning more? Contact our team to see a demo.

