Customers tell us that during an incident, getting to an answer as quickly as possible and containing the threat is their main objective. That’s why Cado is all about Cloud Investigation and Response Automation. It’s what we do.
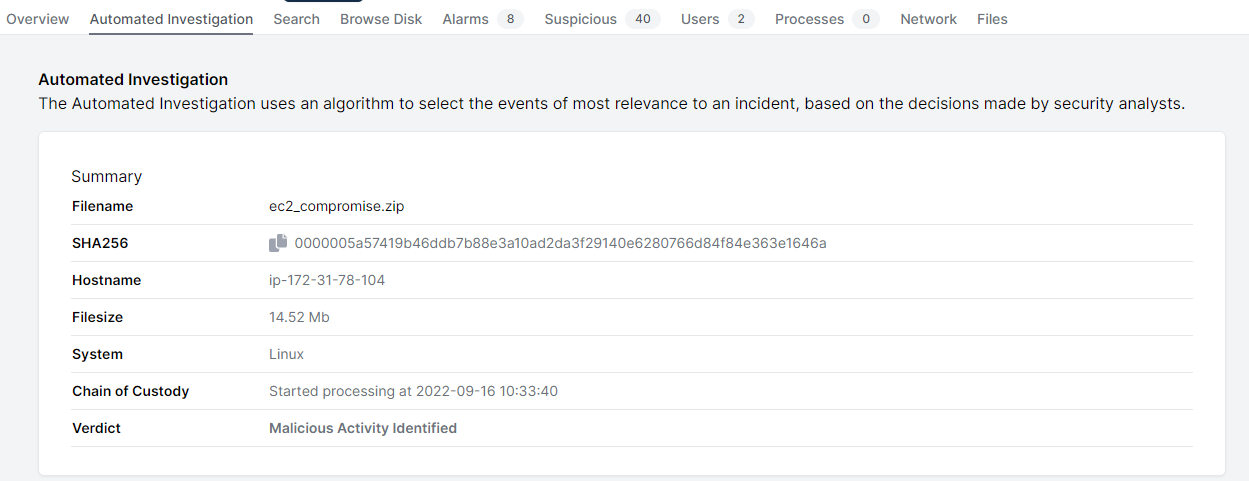
We’ve previously spoken about how you can use Cado for the Automated Collection of data. Now, we’re doubling down on automation by adding Automated Investigations in the latest version of the platform.
With Automated Investigations we replicate some of the common investigative techniques a human analyst would take. We know we’re a long way from replacing a human analyst - but we’re looking to free up their time to focus on the most important incidents by ruthlessly automating where we can.
How Automated Investigations Work
The biggest question an analyst needs to answer in responding to a malware alert is “How did the malware get there?”
A typical process for an analyst looking to answer this question normally focuses on looking for suspicious events either side of the creation of the malware:

In the Cado Response Platform we model Automated Investigation on this typical methodology.
In the example below we can see in the Automated Investigation that a user logon has been included as an event of interest given it was from just before the creation of malware, even though the user login is not suspicious in of itself:

We’ve started to define and implement these automated “pivot points” within Cado Response and will continue to expand them over time. We’re also looking to make the platform more action-oriented, and will be sharing more on Automated Response capabilities soon.
Why you should use Automated Investigations
Typical SOC analysts and Incident Responders need to respond to multiple potential incidents a day. By automating away the first, repetitive, stage of an investigation, you:
- Reduce the amount of time spent investigating each incident. That saves you time, and ultimately cost.
- Reduce the Mean Time To Respond to incidents, which frees up your analysts to focus on the really serious incidents
Try it out!
If you would like to try out Automated Investigations, you can either deploy our free Community Edition or a two week trial of the full product today.

