Back in April 2022, Cado discovered a suspicious ELF binary that utilized DNS over HTTPS, binary padding and in-memory execution to conduct cryptojacking. After analyzing the sample in question, our researchers soon realized that they had encountered the first malware campaign specifically targeting Lambda - AWS’ serverless computing environment.
Despite there being little activity in relation to this campaign since it was first discovered, we’ve recently detected a number of new Denonia samples.
Here are the SHA256 hashes of a few of the recent Denonia samples so other researchers can review them too:
- 148f4644b8351f4af4e8a4f9bad33a24202dda78d7de2d34b1b305378a0c3cc7
- 45bf0903ea780ffafa8f6b361098028aeb0da854ce3c1b9cfcaac4de666e0e8b
- 47f21cbb9245d826f111707284ca2a7b29908cd49aab4dead5e7303fdc5a32b1
- 94264ae80ca8c9875d18477eed4d9212401309ca3394736610440b1ea792a5c0
- c0a5d6c23bf1383aa646c40fa850636e05706f48d5766805cab06dced8768d32
- cb17dd07ce8a9294443f34c5c52e797c744d4c12b009dc9d531bbe17ba7b44cf
- d7474c830abcd365e03bb2458c0abd723b8c2477384861a50aaf34065702b61e
Why do we think these are Denonia?
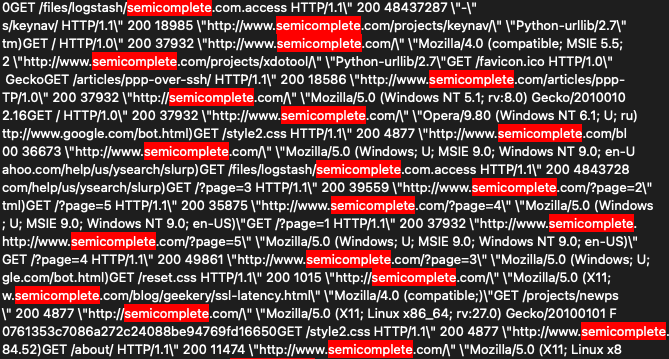
The samples all contain an embedded version of XMRig, which is executed from memory. This is consistent with the original Denonia samples we analyzed. They also include several thousand lines of HTTP request strings, which we determined were used for binary padding in the initial analysis.
Finally, several of the samples have been submitted to VirusTotal from the Philippines, where the original samples were submitted from.
Some Updates...
Each of these samples are ELF binaries, compiled for either ARM64 or x86_64 architectures - both of which are natively-supported by Lambda. These versions employ heavier obfuscation in comparison to the original samples, confusing static analysis tools such as Redress. However, they contain most of the third-party packages required to execute Go-compiled code in Lambda. They also display the following log statement when executed outside the Lambda environment, as the original samples did:
2022/12/14 15:17:25 expected AWS Lambda environment variables [_LAMBDA_SERVER_PORT AWS_LAMBDA_RUNTIME_API] are not defined
Interestingly, these samples do not include the Golang DNS over HTTPS package likexian/doh-go, which was a notable feature of Denonia. This could either be an effort to evade detection, as our own YARA rules published at the time of discovery searched for this package, or it could be that these are actually earlier variants of Denonia - from before the DoH feature was implemented.
At Cado, we’ve built a tool for automating investigation and response in the cloud. Check out our 14-day free trial to see the Cado platform in action. For more information on this topic, take a look at our playbook “Ultimate Guide to Incident Response in AWS”.

