While many organizations have doubled down on cloud security in recent years, most still wrestle with closing the gap between detection and response. Once malicious activity has been identified, it can feel nearly impossible to understand the true scope and impact.
When it comes to incident response, the more data sources you can analyze in aggregate, the better your investigation will be; however, this isn’t easy – especially in the case of complex, multi-cloud environments. In Azure alone there are over 200 products and services, each with their own set of best practices and data sources. Each cloud provider has their own terminology, security tools, monitoring logs, and APIs, making it extremely difficult for analysts to know which data sources are most valuable to capture, how to capture them, and moreover, how to best investigate them.
Naturally, security teams have attempted to apply legacy investigation tools and processes to the cloud, but deep-dive investigations are still too complicated and time consuming. In many cases, analysts need to use a patchwork of legacy and open-source tools and resort to spreadsheets to piece together an investigation. Worse, due to the amount of time and resources required to perform forensics in the cloud, security teams often don’t have the cycles to do an investigation as frequently as they feel is necessary, leaving the organization vulnerable to risk.
Cado’s mission is to provide security teams with a faster and smarter way to perform forensics investigations in the cloud. The Cado platform harnesses automation at its core to expedite the end-to-end incident response process. When it comes to the investigation itself, the platform automatically presents key incident details including a full timeline of events, saving analysts weeks of time that would have been spent in spreadsheets. Cado’s timeline feature provides analysts with a unified view of hundreds of data sources across cloud-provider logs, disk, memory and more. Further, the Cado timeline supports cross-cloud evidence items to be viewed in a single pane of glass in cases where an incident spans multiple public cloud environments. This level of contextual awareness is vital in understanding the impact and scope of an incident.
As part of this latest product release, Cado has introduced additional enhancements to its timeline feature to help security teams further supercharge investigations and reduce Mean Time To Response (MTTR). Here’s an overview of the most recently released timeline functionality:
New Timeline View
Cado is excited to have revamped the look and feel of the timeline feature so that it is more intuitive to navigate and pivot off key artifacts during an investigation. From card view to a powerful tabular view, we hope this will greatly streamline the analysis process. This new view also aligns with our mission to make forensics more approachable so that analysts of all levels can perform incident response in the cloud.
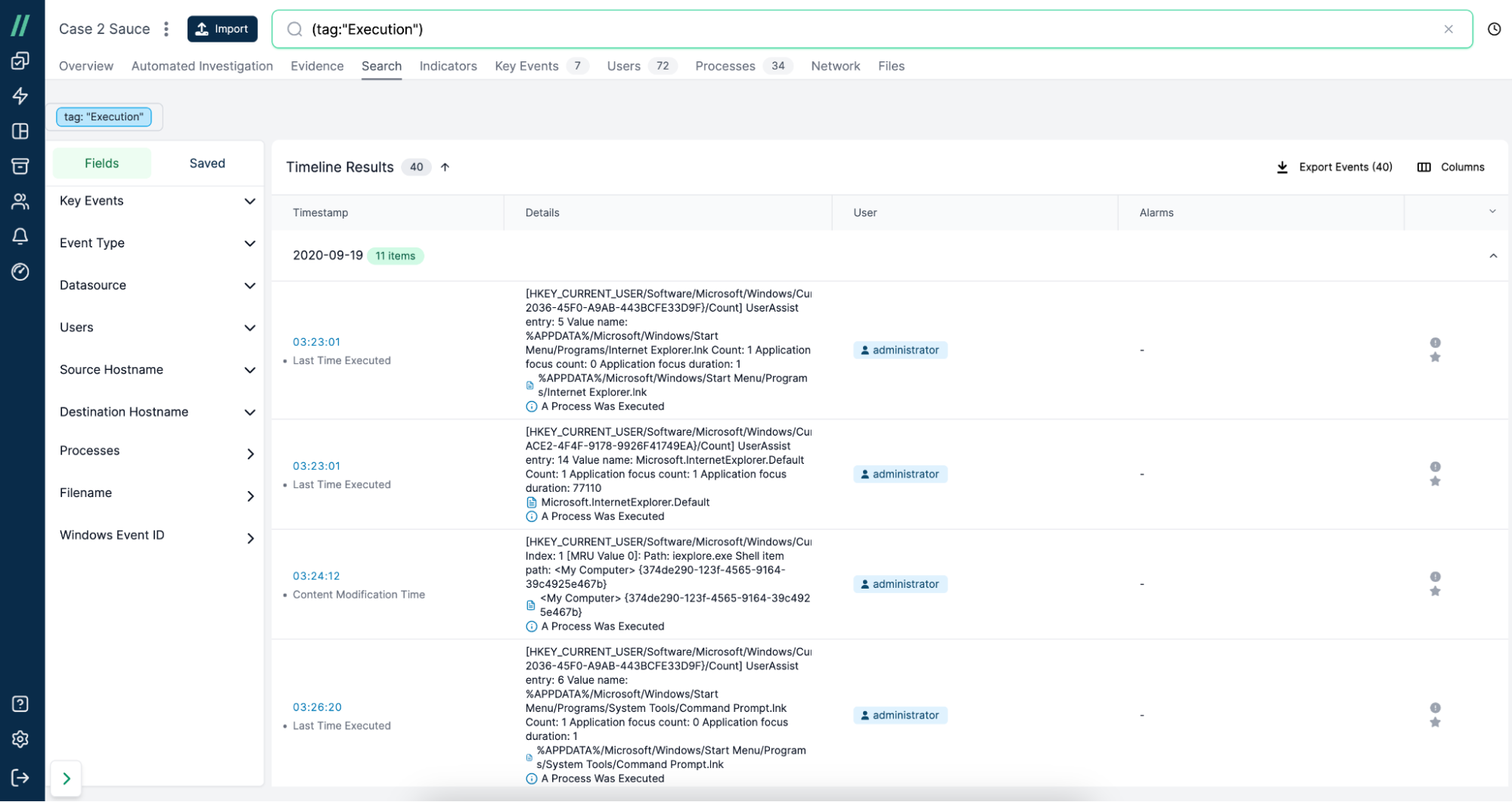
Cado Timeline
Faceted Search
Faceted search will allow users to narrow down their search results quickly using facet options, which represent categories of data. The facet options Cado presents will provide awareness to the user on the core data types/ attributes the events contain, enabling them to refine datasets quickly and efficiently using the facet navigation, rather than having to add filters to their query in the search bar manually, which can burden the user.
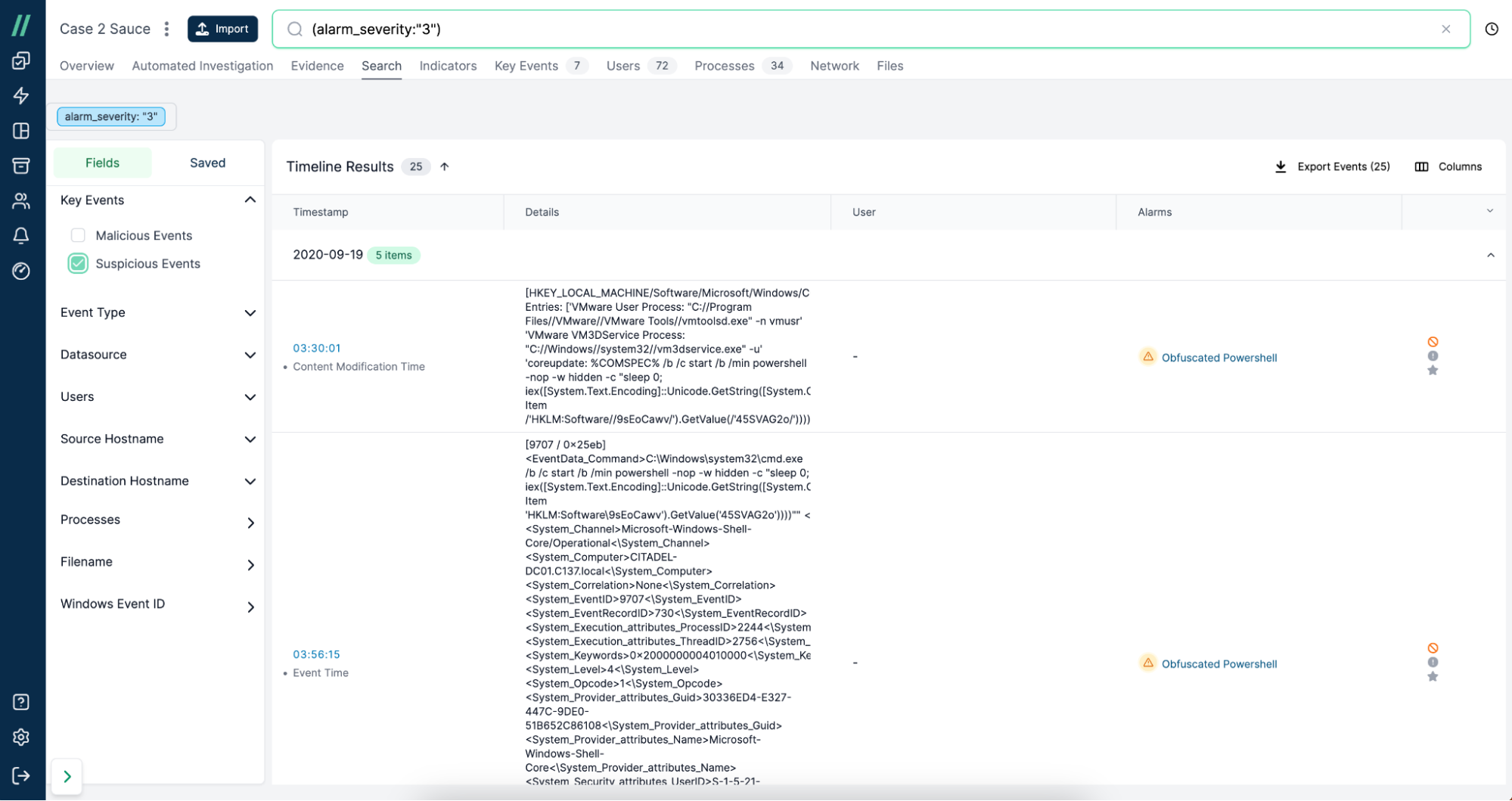
Cado Faceted Search
Saved Search
Saved search will allow users to save investigation queries for re-use at a later date. During an investigation, particularly in the earlier analysis phases, a user will be exploring and pivoting across datasets and will have naturally built-up a considerable query in the search bar. Users can now preserve this query so they can re-execute it on their next session (or even share it with colleagues). This feature will save precious investigation time by not having to rebuild a query from scratch, thus enabling rapid search and visibility.
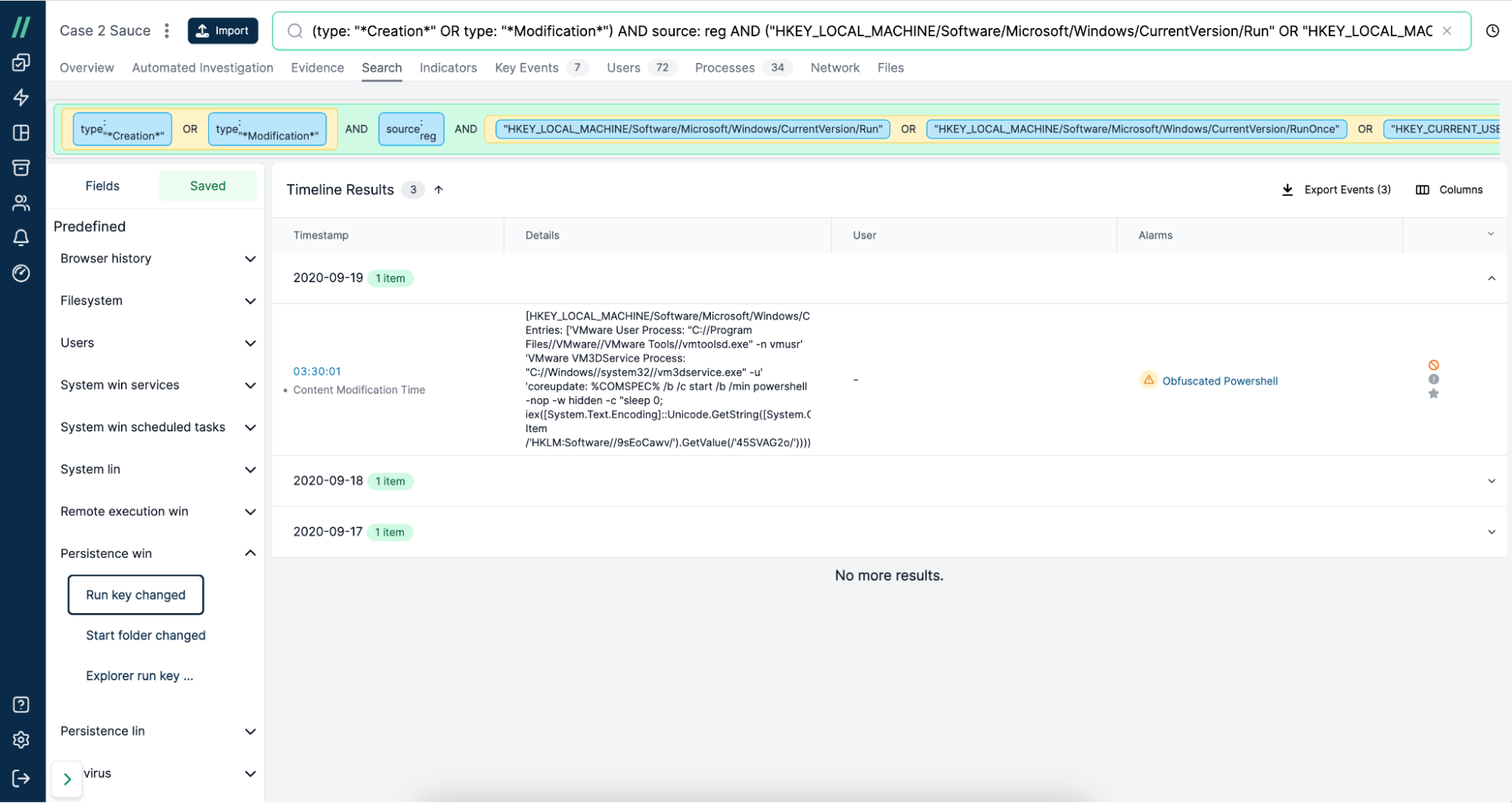
Cado Saved Search
See for Yourself
Take a live tour of Cado's new timeline feature:
If you're interested in learning more, reach out to our team or take advantage of a 14-day free trial.

