
Decoding the NIST Cloud Computing Forensics Reference Architecture
It’s been a busy few months for cloud forensics:
- Gartner released their first report on the space Cloud Investigation and Response Automation
- We’ve seen leading cloud security players start to offer the ability to capture forensic data for processing in platforms like Cado
- The new SANS 509 course “Cloud Forensics & Incident Response” is clearly popular, based on the number of people posting the related GIAC GCFR certification on LinkedIn.
- NIST, the US Standards Agency, released their draft “NIST Cloud Computing Forensic Reference Architecture” in February
This blog discusses the NIST Cloud Computing Reference Architecture, as we haven’t seen much discussion on that. Read on for a brief history in NIST Cloud Forensics.
Cloud Computing Forensic Workshop - 2014
Much of the initial kick off of cloud forensics from NIST started with the “Cloud Computing Forensic Science Workshop” a decade ago in 2014. Check out this retro poster:
NIST Cloud Computing Forensic Science Challenges - 2020
Off the back of this was the publication “NIST Cloud Computing Forensic Science Challenges”, which entered draft in 2014 and only made it to final publication in 2020.
At a high level, the challenges identified include:
- Difficulties with the nature and variety of Architectures in different Cloud Service Providers (CSPs)
- Data collection issues, due to lack of access and even locating where data might reside
- Correlating data and timestamps between various types of data
- Anti-Forensics
- Identifying who owns data, and how to authenticate access to it
- Legal issues accessing data, where the physical location and jurisdiction isn’t clear
- Lack of standard operating procedures for collecting forensic data in the cloud
- Lack of training and knowledge of cloud-specific forensic issues
NIST Cloud Computing Forensic Reference Architecture - 2023
The forensic reference architecture is not a light read. Perhaps the best summary is this section, which outlines the motivations for the forensic reference architecture:
Cloud System Architects and Engineers:
This target audience might ask: “To what extent does the cloud system I’m designing facilitate the use of digital forensics?” The architectural methodology and initial architecture presented in this paper can help this audience identify where there could be potential challenges for conducting forensics and can allow them to focus on areas of potential concern. System trade-offs can be considered as well (e.g., the more that a system facilitates the use of forensics, the greater the negative operational or economic impacts might be, or the greater the chance that privacy might be impacted negatively).
Forensic Practitioners:
This target audience might ask: “What items do I need to be aware of to conduct digital forensics in the cloud environment versus a traditional or on-premises computing environment?”
Consumers Who Want to Procure Cloud Services from Providers:
This target audience might ask: “What forensic questions and issues do I need to consider when discussing what a cloud provider has to offer?”
While the document describes the motivation for the reference architecture, most of the “meat” is actually in the associated spreadsheet “Forensic Reference Architecture Data Set”, and in particular the tab labelled “Challenges”.
Some of these challenges don’t seem particularly forensic, and frankly a little odd. For example:
- The cloud offers computing power that would otherwise be unavailable to criminals with small budgets and/or limited resources
- The distributed nature of cloud computing enables a criminal organization to maintain small cells of operation with no one cell knowing the identity of any others
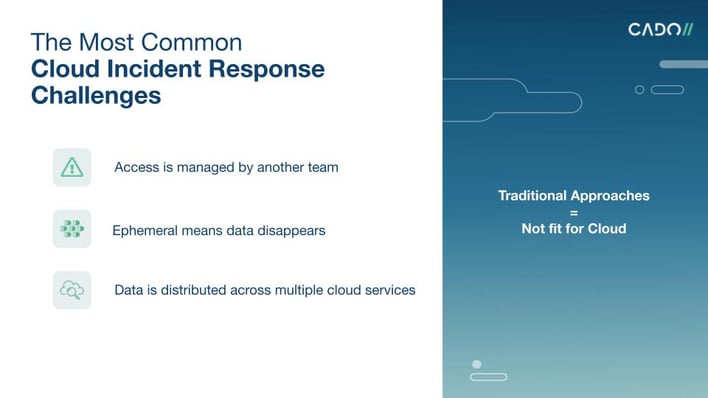
However most track closely to the issues our own customers talk to us about, in particular:
Governance
- Decreased access and control of data at all levels by cloud Consumers
- Reliance on cloud Providers
- Authentication and access control
- Lack of training materials
Collection and Preservation
- Segregation of potential evidence in a multi-tenant system
- Chain of custody of data
- Locating and collecting cloud- based data for forensic investigations
- Data associated with deallocated virtual machine (VM) instances may only be available for a limited time
- Identifying storage media where artefacts, log files and other evidence may be found
- Imaging in the cloud
Processing and Analysis
- Evidence correlation across cloud Providers
- Unification of log formats
- Evidence correlation across cloud Providers
- Unification of log formats
- Segregation of potential evidence in a multi-tenant system
- Chain of custody of data
- Decreased access and control of data at all levels by cloud Consumers
- Locating and collecting cloud- based data for forensic investigations
- Data associated with deallocated virtual machine (VM) instances may only be available for a limited time
- Identifying storage media where artefacts, log files and other evidence may be found
- Imaging in the cloud
- Reliance on cloud Providers
- Authentication and access control
- Lack of training materials
Indeed, the challenges we outline in our introductory presentations of Cado unsurprisingly align closely:
If you would like to see how Cado Security can help you solve your Cloud Computing Forensic Challenges - check out our free trial or request a demo.
